
It only takes a few minutes for someone to fall victim to an online phishing scam. But what can we do if we click on a link and suddenly realize it might be a scam?
Provided by global digital security company ESET Ten steps we can take after we take the bait We have fallen victim to online phishing scams.
- We do not give more information. If we receive an email from an online store that raises some suspicion, but we click on the attached link, we avoid sharing any additional information and do not give out our bank account details.
- We disconnect our devices from the Internet. Some phishing attacks may install malware, collect information about us and our devices, or remotely control the compromised device. To mitigate the damage, we start by disconnecting the compromised device from the Internet.
- We back up our data.
Disconnecting from the Internet will prevent further data from being sent to the malicious server, but what about our data is still at risk? We should back up our files, especially sensitive documents or files with high personal value, such as photos and videos. Of course, backing up our data after an attack can be dangerous, as it may have already been compromised by malware and we are backing up the malware as well. That’s why we should back up our files regularly and proactively. If malware infects our devices, we can recover our data from an external hard drive, USB stick, or cloud storage service.
- We implement it A command to scan for malware and other threats Use anti-malware software from a trusted provider while the device is still offline. Ideally, it would be useful to perform a second scan using, for example, ESET’s free online scanner. If the scanner finds suspicious files, we follow the instructions to remove them.
- We are looking forward to it Factory reset possible, That is, returning our devices to their original state by removing all installed applications and files. However, some types of malware may remain on the device even after a full reset, but scanning our mobile device or computer will likely successfully remove any threat. Factory reset cannot be undone and will delete all locally stored data, so we must have backups.
- We change our passwords. Phishing emails can trick us into revealing our sensitive data, such as ID numbers, bank and credit card details, or passwords. Even when we do not give out our information, it is possible that if malware is installed on the device, it will detect it. If so, we should immediately change our login details to different accounts.
- We communicate with banks, authorities and service providers If we provide our bank/credit card details or login details to a website that can access our cards. The card may be blocked or frozen to prevent future fraud and to prevent or reduce any financial losses.
- We monitor our activity on the accounts.
Cybercriminals who successfully break into one of our devices or accounts may try to prove that they have been there for as long as possible. They may change their login details, email addresses, phone numbers or anything else that may help them establish their credentials in our account.
We monitor our activity on our social media accounts, banking information and online purchase history. For example, if we detect payments that appear strange, unknown, or unauthorized, we report them, change our login details, and request a refund.
- We are looking for unknown devices. If hackers stole our account information, they likely tried to log in from their own devices. Most social networking platforms keep a log of your current login sessions as part of their privacy settings. We check this and perform forced disconnection for every unknown device.
- We notify friends, contacts, service providers and our employer, where scammers sometimes use our contact list on a compromised account to spread phishing links or spam. We take steps to prevent others from falling victim.

“Avid problem solver. Extreme social media junkie. Beer buff. Coffee guru. Internet geek. Travel ninja.”




More Stories
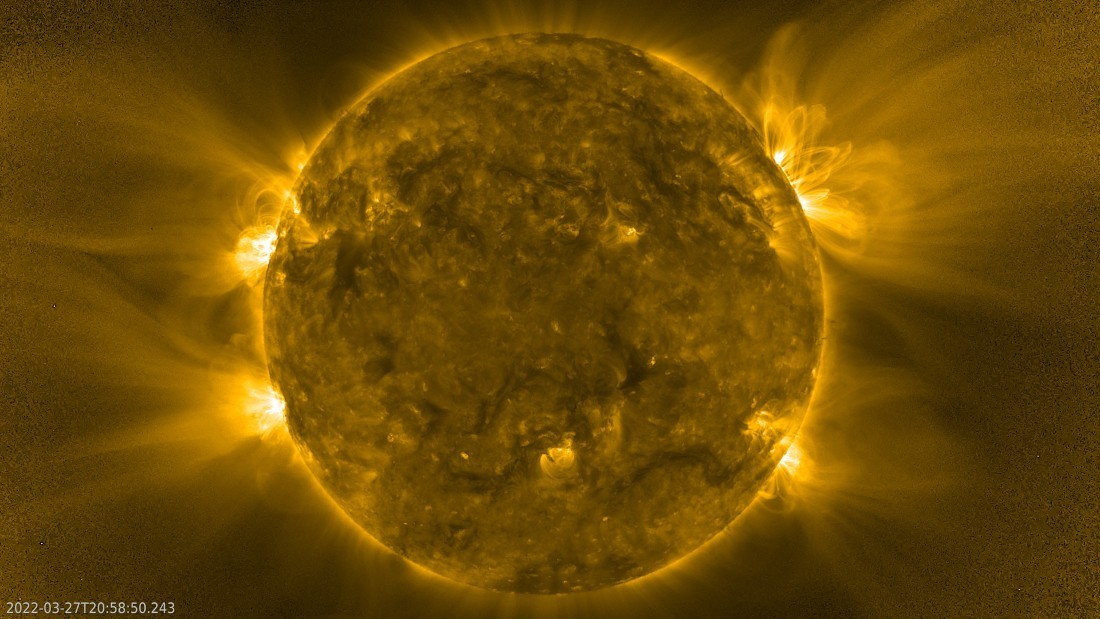
Solar rain, explosions and the sun’s thin ‘crown’ recorded by the solar lander: a bizarre landscape at a million degrees Celsius [video]
Helldivers 2: A huge trend with more than 85 thousand negative reviews in a few hours
Shogun: Not a Typical Game of Thrones Set in Feudal Japan – Definitive Review